Flipper Zero A Security Researcher's Analysis of IoT Product Vulnerabilities
What is a Flipper Zero? It's a pocket-sized multi-tool, cleverly disguised as an electronic pet, designed for secu

What is a Flipper Zero? It's a pocket-sized multi-tool, cleverly disguised as an electronic pet, designed for security researchers and engineers. This powerful device uncovers widespread security flaws in everyday IoT products by interacting with their wireless protocols. A security researcher’s analysis demonstrates how the Flipper Zero highlights these vulnerabilities and why understanding them is crucial for future IoT security. The Flipper Zero is a critical tool for comprehending these risks.
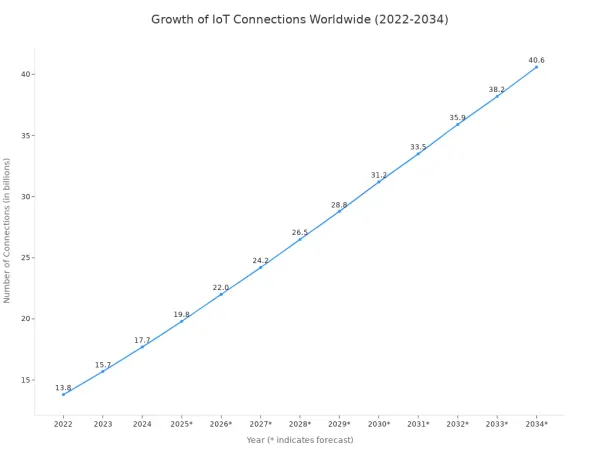
Note: IoT device adoption is expected to surge to 40.6 billion by 2034, making device security more important than ever.
Key Takeaways
- The Flipper Zero is a small tool that helps find security problems in everyday smart devices.
- It can copy signals from things like garage door openers and access cards to show how easily they can be hacked.
- The Flipper Zero helps people learn about cybersecurity in a fun, hands-on way.
- It shows that many smart devices and public systems have old, weak security that needs to be updated.
- While powerful, the Flipper Zero cannot break strong, modern security like advanced encrypted cards.
What is a Flipper Zero: An All-in-One Tool

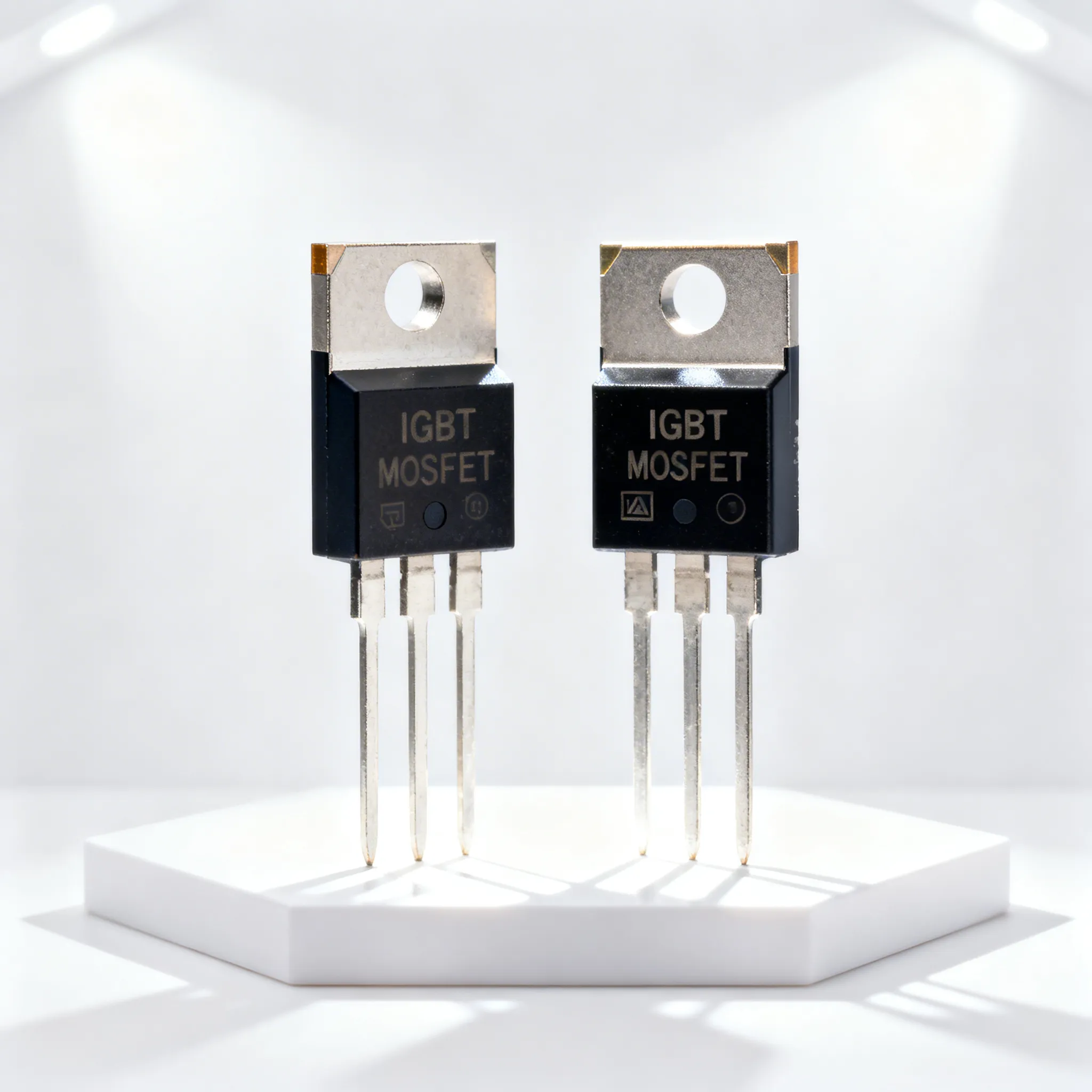
So, what is a Flipper Zero? It is a compact, multi-functional hardware hacking tool that consolidates numerous testing instruments into a single physical device. At its heart, the Flipper Zero runs on a powerful and efficient STM32WB55RG microcontroller. This chip features a dual-core architecture with both an ARM Cortex-M4 and an ARM Cortex-M0+ processor, providing robust capabilities for both applications and radio protocols like Bluetooth. This gadget is often called a hacker swiss army knife for its versatility.
Sub-1 GHz Radio and Replay Attacks
The Flipper Zero includes a Sub-1 GHz radio antenna. This component allows the device to interact with wireless systems operating in the 300-928 MHz frequency range, such as garage door openers, remote keyless systems, and IoT sensors. A security researcher can use the Flipper to capture and analyze these signals. For systems without rolling code protection, the Flipper Zero can record a signal and re-transmit it later. This technique, known as a replay attack, demonstrates a serious security flaw. This hacking/testing tool makes it easy to test for such vulnerabilities.
NFC & RFID for Access Control
The Flipper is also equipped with antennas for Radio Frequency Identification (RFID) and Near Field Communication (NFC). It can interact with both low-frequency (125 kHz) and high-frequency (13.56 MHz) cards. The Flipper Zero can read, save, and emulate many types of access cards, making it a powerful tool for auditing physical security.
Flipper Zero Card Compatibility The Flipper supports various card types, highlighting its broad capabilities.
Card Type Read Emulate Clone (Save) Mifare Classic ✅ ✅ ✅ NTAG-21X ✅ ✅ ✅ EM4100 ✅ ✅ ✅
Infrared (IR) Universal Remote
Another feature of the Flipper is its infrared transceiver. The Flipper Zero can learn IR signals from any existing remote control. After learning, the Flipper can act as a universal remote for countless devices, including TVs, air conditioners, and audio systems. This function shows how many consumer electronics rely on simple, unencrypted IR signals for control, making them easy to manipulate with the right tool. The Flipper can become your one remote for everything.
Advanced Hardware Interaction
Beyond wireless protocols like Bluetooth or WiFi, the Flipper Zero offers advanced hardware interaction through its GPIO pins. These pins allow the device to connect directly to other hardware components for debugging, testing, and control. The Flipper can also function as a USB to UART/SPI/I2C bridge, a critical function for hardware hacking and analysis. This turns the Flipper from a simple remote into a comprehensive development and testing platform, expanding beyond WiFi and Bluetooth. What is a Flipper Zero? It is a complete package for hardware exploration.
Exposing Real-World Security Flaws

The Flipper Zero is more than a collection of tools. It is a practical device for demonstrating security weaknesses in the real world. A researcher can use the Flipper to make abstract vulnerabilities tangible. This process shows how easily insecure systems can be compromised.
Insecure Physical Access Systems
Many buildings use outdated technology for physical access. The Flipper Zero excels at exposing these flaws. For example, it can interact with low-frequency (125kHz) keyless entry cards commonly used for office doors. A researcher can hold the Flipper near a card, read its data, and save it. The Flipper can then emulate the card to unlock the door, showing a major security risk.
Many of these systems rely on the Wiegand protocol, an old and insecure standard.
- The protocol was made in the 1980s and has no encryption.
- Attackers can easily intercept and replay its signals.
- Basic HID cards use a fixed number that the Flipper can read from the RFID signals.
- Even modern readers are vulnerable if they use the Wiegand protocol for data transfer.
The Flipper also tests Sub-GHz systems. In one test, a researcher used a standard Flipper Zero to target a gate's key fob. The device successfully captured the fob's signal from up to 35 feet away. The researcher then replayed the signal with the Flipper to open the gate. This proved that unauthorized entry was possible. The Flipper could even find and capture the signal from 20 feet away without knowing the exact frequency first.
Smart Home & IoT Vulnerabilities
Smart homes are filled with connected devices, but not all of them are secure. The Flipper Zero can perform replay attacks against vulnerable smart home products. A replay attack happens when an attacker records a wireless command and sends it again later. This can trick a device into performing an action, like turning on or off.
Vulnerability Spotlight: Replay Attacks 🕵️ A replay attack is like recording someone saying a password and playing it back to gain access. If a device doesn't check if a message is new, it can be fooled by an old, recorded command. The Flipper makes it easy to capture and replay these commands.
For instance, some smart light bulbs, like the TP-Link Tapo L530E, are vulnerable to this. The bulb's communication protocol lacks proper message freshness checks, such as timestamps or sequence numbers. A person with a Flipper can eavesdrop on the wireless signals sent to the bulb. They can record the "turn on" command and replay it anytime, demonstrating a significant flaw. This cryptographic weakness means an attacker can control the device by replaying old messages.
Legacy Systems in Public Spaces
Public spaces often contain legacy systems that have not been updated in years. These systems can include digital information kiosks, older payment terminals, or public utility controls. The Flipper Zero is an excellent tool for auditing the security of this forgotten infrastructure. A researcher can use its infrared functions to interact with old displays or its Sub-GHz radio to probe remote-controlled barriers. The versatile nature of the Flipper allows it to test a wide range of protocols. This testing reveals that many systems in public view operate on simple, unencrypted signals, making them easy targets for manipulation or disruption. This highlights a critical need for ongoing security assessments of all public-facing technology, not just new products.
A Security Researcher's Perspective
From a professional viewpoint, the Flipper Zero is a fascinating device. It occupies a unique space between a hobbyist gadget and a professional instrument. Security researchers see its value and its limits.
The Flipper Zero as an Auditing Tool
The Flipper Zero is a valuable auditing tool for initial security assessments. Penetration testing providers like Vumetric use the Flipper to simulate real-world attacks. This testing helps organizations find and fix weaknesses. The device excels at:
- Cloning insecure RFID access cards.
- Finding IoT vulnerabilities through replay attacks.
- Performing wireless reconnaissance.
Professional firms, such as the HiSilicon-authorized solutions partner Nova Technology Company (HK) Limited, understand that a comprehensive penetration audit requires a diverse toolkit. The Flipper is excellent for quick, on-the-go assessments. Penetration tester Kyser Clark notes the Flipper is a great gateway into cybersecurity for beginners.
Democratizing Security Education
The Flipper makes complex security concepts accessible to everyone. Its user-friendly interface helps students and hobbyists learn through hands-on experience. For example, the 'Flipper Zero: Microsoft Project-Based Learning Program' used the device to teach cybersecurity principles. Students used the Flipper to:
- Verify or debunk claims about the Flipper Zero on social media.
- Capture and analyze signals from smart home devices.
- Study signals from smartphones to understand potential vulnerabilities.
This practical approach makes learning about wireless protocols and hardware hacking engaging and effective. What is a Flipper Zero? It is an educational bridge to a technical world.
Understanding the Tool's Limitations
While powerful, the Flipper Zero has clear limitations. It is not a master key for all systems. More specialized tools often outperform the Flipper in specific domains.
| Feature/Tool | Flipper Zero | HackRF One | Proxmark3 |
|---|---|---|---|
| Primary Function | All-in-one (RFID, RF, IR) | Software-defined radio (SDR) | Advanced RFID/NFC tasks |
| Portability | Highly portable, standalone | Requires a computer | Often requires a computer |
| Ease of Use | Simple, user-friendly | More complex | More complex |
The Flipper struggles against modern encryption. It cannot break the security on systems like:
These systems use strong cryptographic protections that prevent the Flipper from cloning them. Similarly, the device cannot defeat modern rolling codes like KeeLoq without the correct manufacturer key. This shows that while the Flipper is a versatile gadget, robust security measures effectively counter it.
The Flipper Zero makes abstract vulnerabilities tangible. This flipper demonstrates real-world risks for any insecure device. It is a critical wake-up call for manufacturers. They must prioritize robust security protocols like AES-256 encryption and rolling codes. The Flipper Zero shows why this matters. Ultimately, the flipper is a reminder that proactive design is essential in our connected world. The flipper makes these issues clear, and this flipper is a powerful tool.
FAQ
Is the Flipper Zero legal to own?
Yes, owning a Flipper Zero is legal in most places. The device is a tool for security testing and education. However, using it to access systems without permission is illegal. Users must follow local laws and use the device responsibly.
Can the Flipper Zero hack WiFi or Bluetooth?
The Flipper Zero's main radio works on Sub-GHz frequencies. It does not have built-in hardware to hack modern WiFi networks. It has limited Bluetooth Low Energy (BLE) capabilities for testing but is not a primary tool for Bluetooth attacks.
Is the Flipper Zero a good tool for beginners?
Yes, the Flipper Zero is excellent for beginners. Its game-like interface makes learning about cybersecurity concepts fun and interactive. It provides a hands-on way to understand wireless protocols, hardware, and security principles without needing deep technical knowledge to start.
Can the Flipper Zero copy all access cards?
No, the Flipper Zero cannot copy all cards. It works well on older, insecure RFID systems like EM4100 and MIFARE Classic. It cannot clone modern, encrypted cards like MIFARE DESFire or HID iCLASS, which use strong security measures to prevent cloning.